Black Ops Analysis
A technical retrospective on the infrastructure, security protocols, and operational history of the Black Ops Darknet marketplace.
Executive Summary
Black Ops Darknet emerged as a specialized hidden service operating within the Tor network anonymity layer. Distinguished by its strict adherence to walletless transaction models and mandatory PGP encryptions, the platform was designed to facilitate the exchange of digital goods and services in a decentralized manner.
Unlike predecessors that utilized centralized escrow wallets prone to seizure or exit scams, the Black Ops architecture employs a multi-signature framework. This ensures that funds are locked on the blockchain (primarily Monero for privacy) and can only be released when consensus is reached between the participating parties.
The platform has positioned itself as a "hardened" target, utilizing advanced DDoS mitigation filters at the entry nodes and rotating onion addresses to maintain uptime during network stress events.
Technical Architecture
Network Security
Utilizes V3 Onion Services with client authorization protocols. The backend is distributed across multiple geographically isolated nodes to prevent single points of failure.
Cryptocurrency
Primary support for Monero (XMR) utilizing Ring Confidential Transactions (RingCT) to obfuscate sender, receiver, and transaction amounts. Bitcoin (BTC) is supported via optional mixers.
Encryption
Mandatory 4096-bit RSA keys for 2FA login. All communications within the internal messaging infrastructure are end-to-end encrypted by default.
Availability
Custom-built anti-DDoS "EndGame" filters that require proof-of-work challenges before establishing a Tor circuit connection, mitigating layer 7 attacks.
Interface Archive
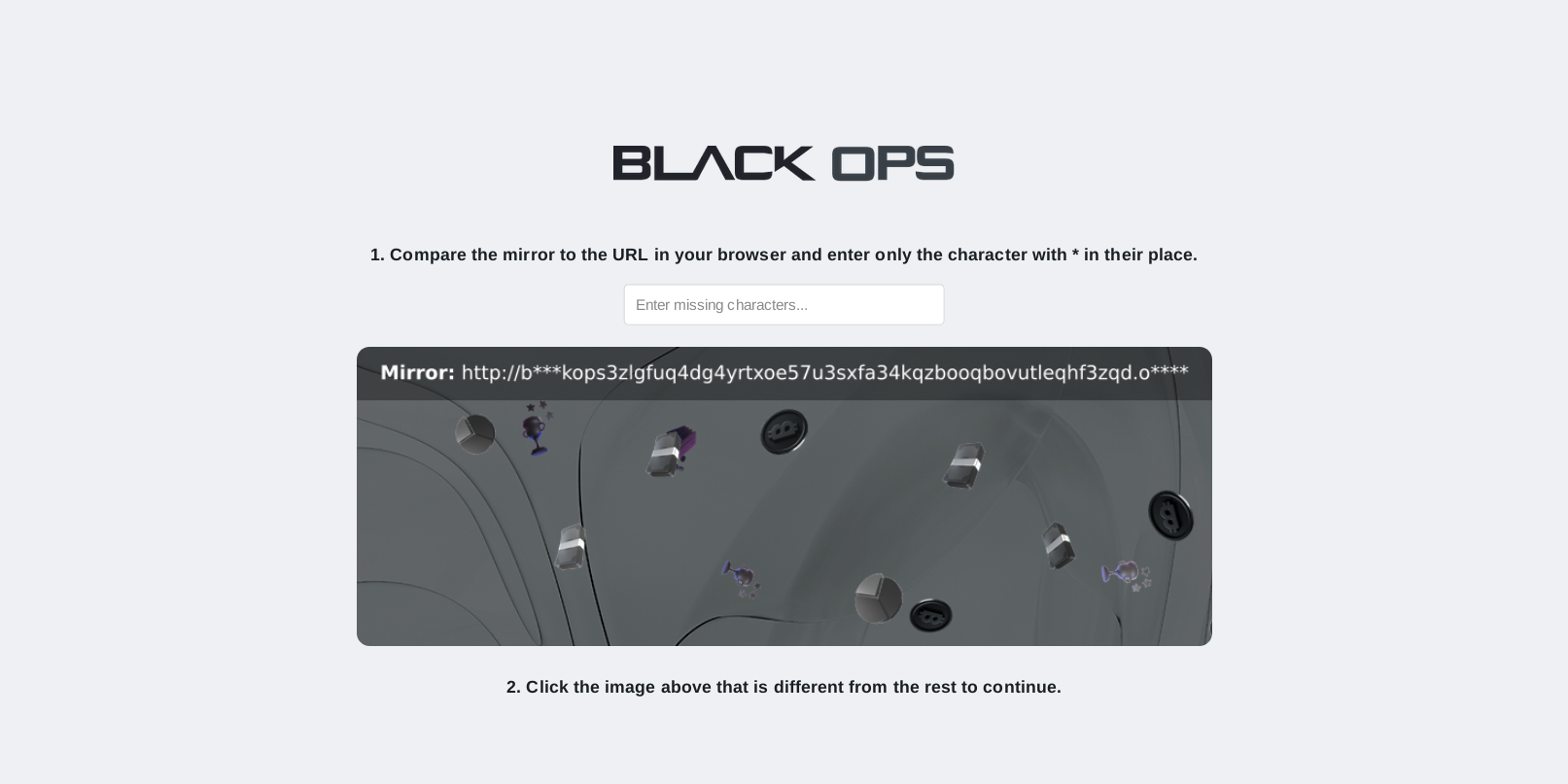
Fig 1. DDoS Filter
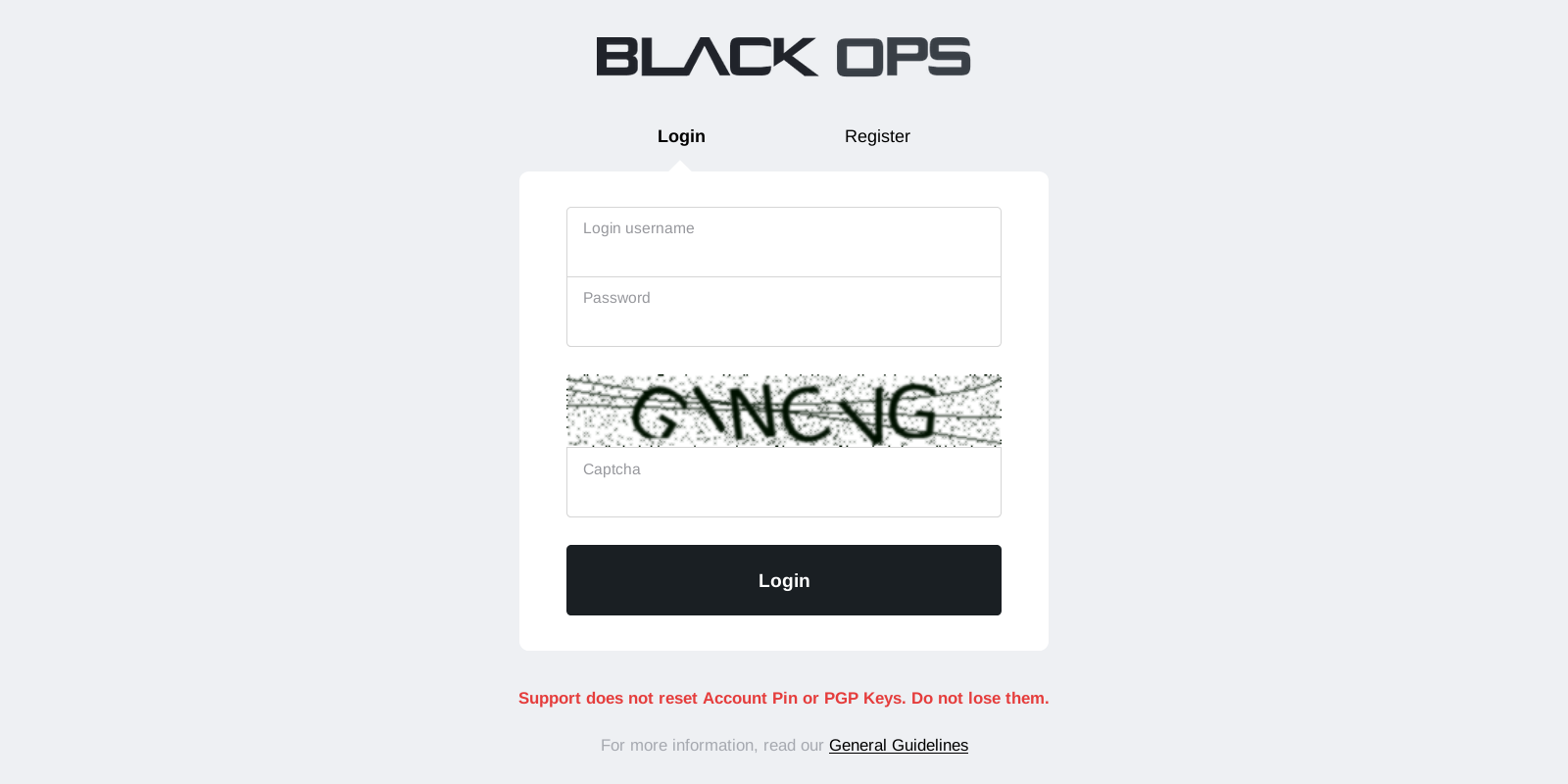
Fig 2. Login Mechanism
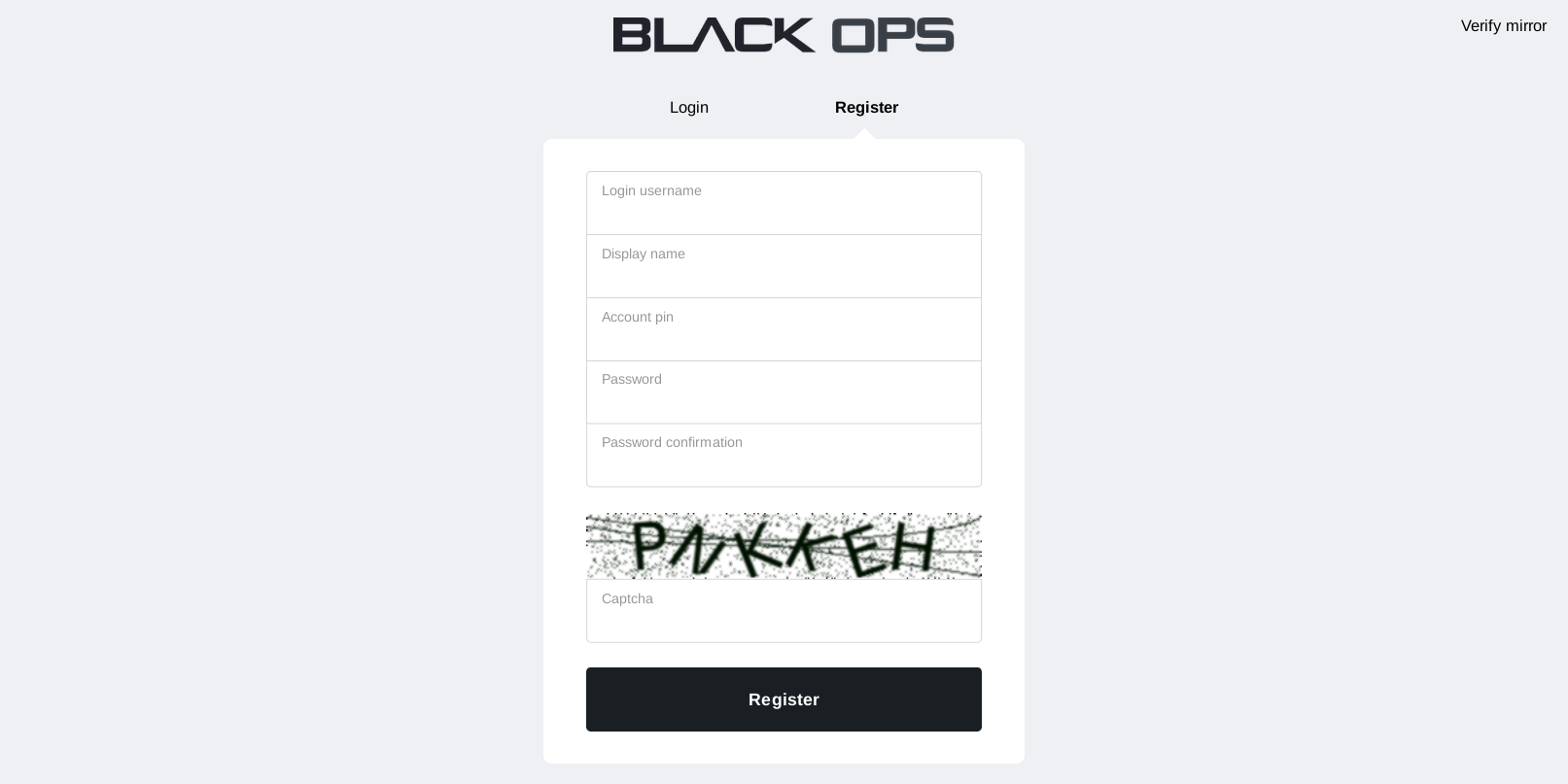
Fig 3. Registration
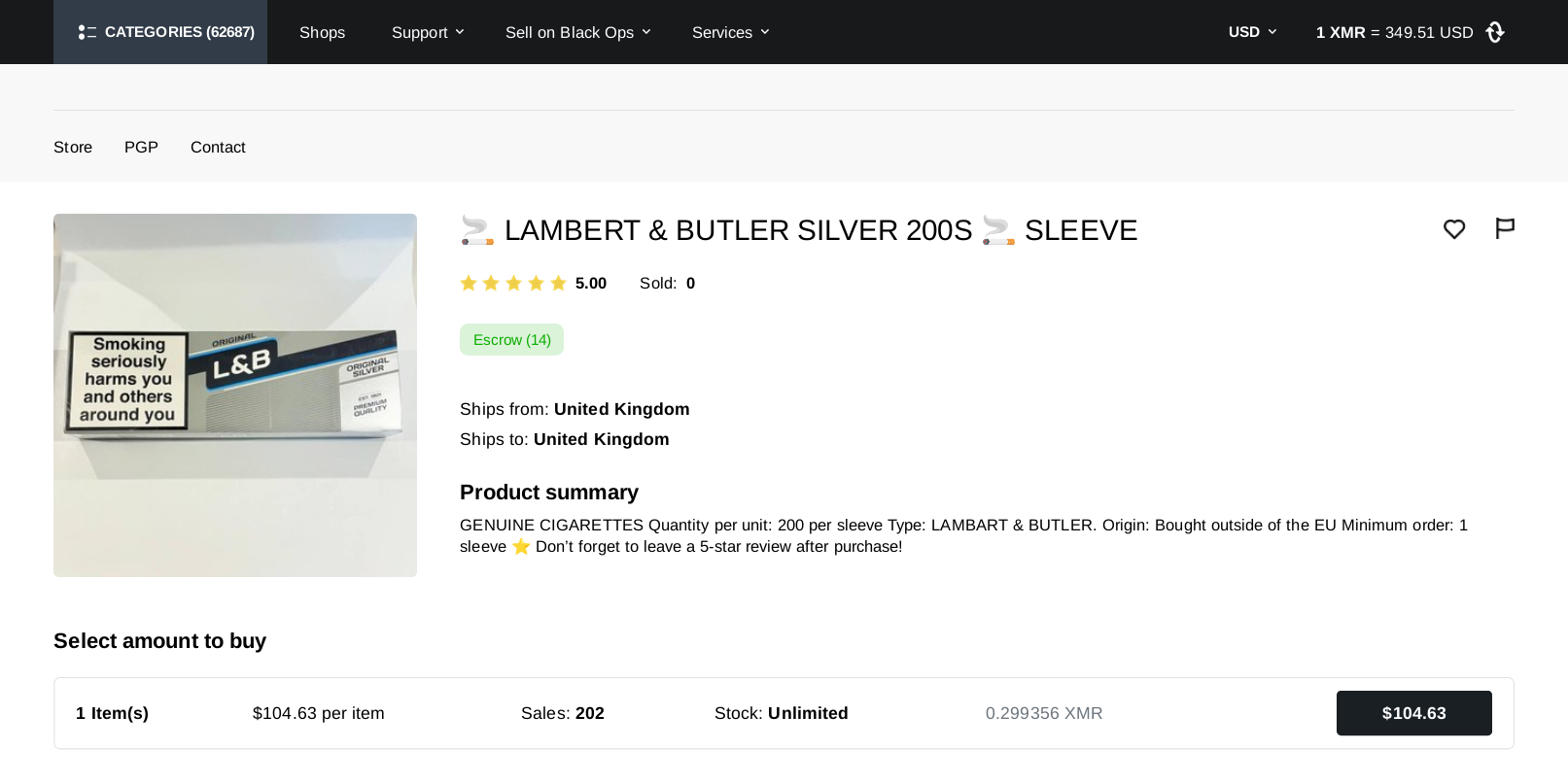
Fig 4. Dashboard